What happened
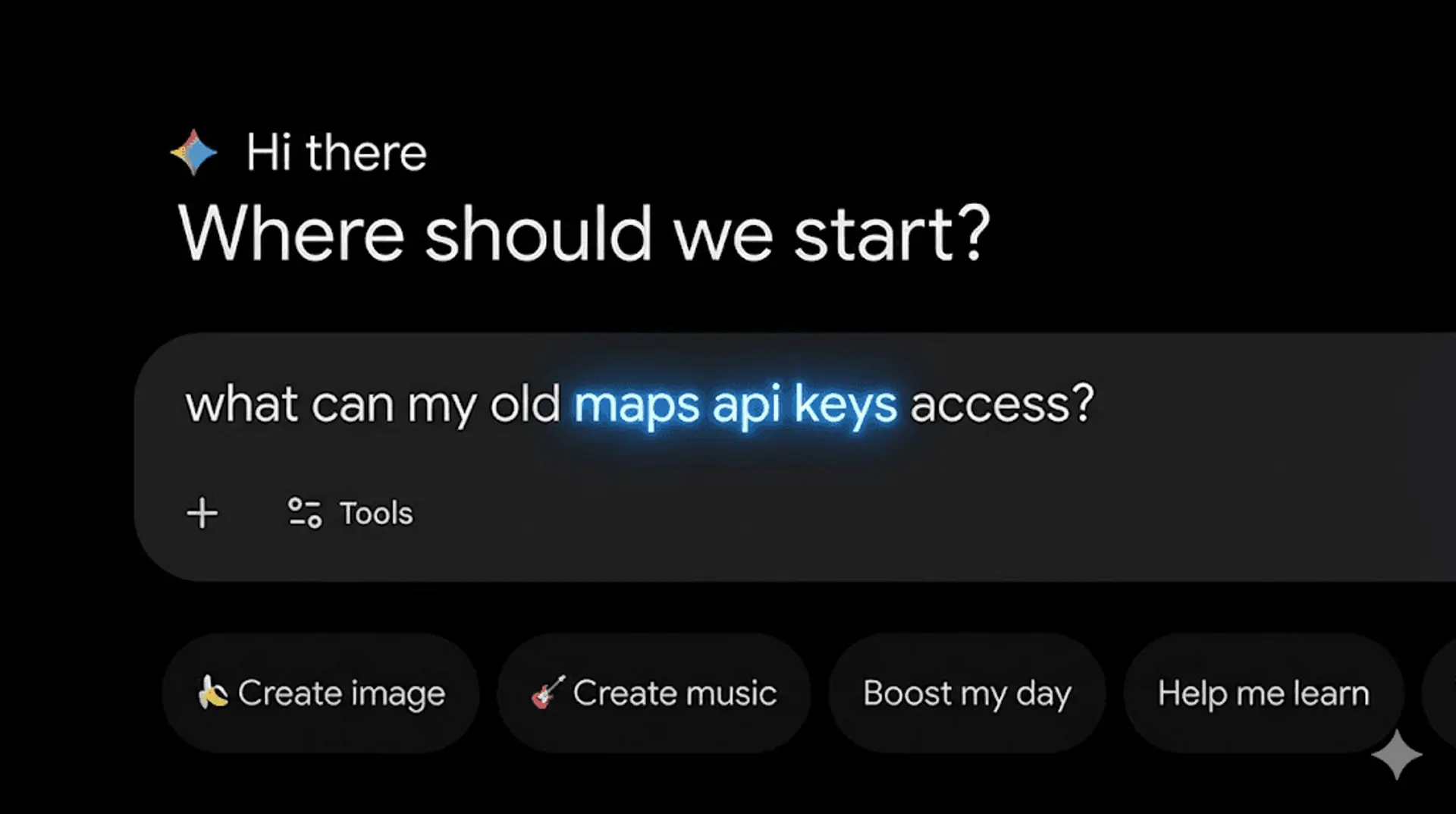
Google API keys, previously designated as non-sensitive public identifiers for services like Maps and Firebase, now authenticate to the Gemini API. This change occurs without warning when the Gemini API is enabled on a Google Cloud project, retroactively expanding privileges for existing public keys and defaulting new keys to unrestricted access. Truffle Security identified 2,863 such vulnerable keys in the November 2025 Common Crawl dataset, including some from Google's own infrastructure, proving the architectural shift from public identifier to sensitive credential.
Why it matters
Security architects and platform engineers face immediate, unannounced risk: publicly exposed API keys, once benign, now function as sensitive credentials. This mechanism allows attackers to access uploaded files and cached content via Gemini endpoints, and generate thousands of dollars in fraudulent API usage daily, impacting project budgets and quotas. The implicit trust upgrade and insecure default posture mean teams must audit all existing Google API keys, especially older ones, to prevent unauthorised data access and unexpected expenditure.
Subscribe for Weekly Updates
Stay ahead with our weekly AI and tech briefings, delivered every Tuesday.